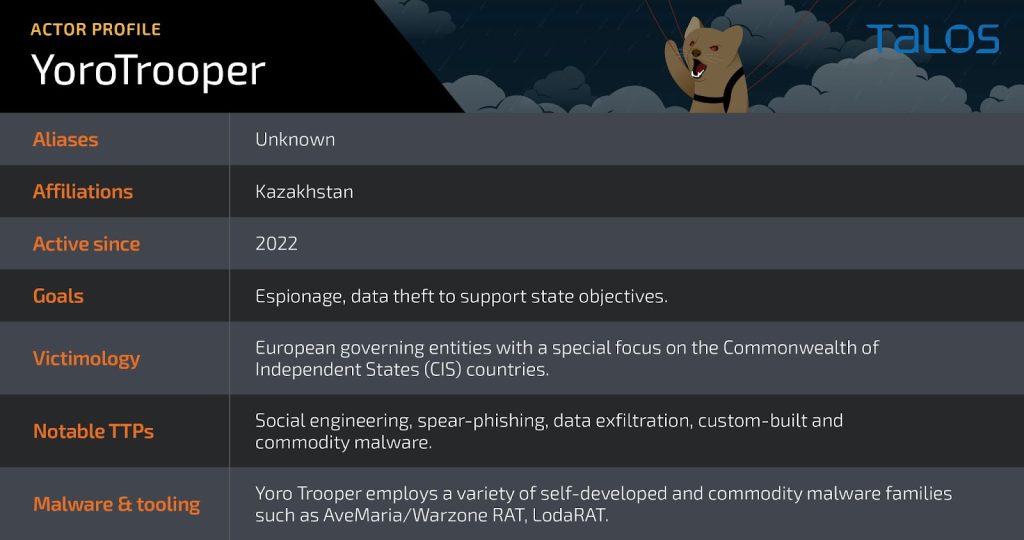
A new report from the Cisco Talos group this week, researchers detail how YoroTrooper, a cyberespionage group likely from Kazakhstan (based on language and currency use), has been active since June 2022 targeting governments in CIS countries. Despite obfuscating their origins through tactics like using Azerbaijani VPNs, they’ve compromised government websites and officials’ accounts. Their attacks rely on a mix of pre-existing malware, custom tools, and phishing emails to steal credentials, with a recent shift towards more sophisticated custom malware written in various programming languages.
The link to Kazakhstan comes from the targets that the group has gone after. In the past year, the group has targeted former Soviet states which would align to Kazakhstan’s objectives.
From the Cisco Talos Blog:
YoroTrooper’s targeting of government entities in these countries may indicate the operators are motivated by Kazakh state interests or working under the direction of the Kazakh government. It is also possible, however, that the actors are simply motivated by financial gain achieved by selling restricted state information. Talos is pursuing further research on YoroTrooper’s intelligence collection goals to ascertain the group’s potential state sponsorship.A number of prominent and successful YoroTrooper intrusions took place in recent months, beginning in June 2023 when the adversary compromised a Tajiki national. Although we could not determine the identity of the victim, Talos assesses that the victim is associated with the Tajik government, based on the nature of the data that YoroTrooper exfiltrated from them, which amounted to 165MB of documents. Many of these documents consisted of government certificates and affidavits, appearing to belong to someone who has visibility into government personnel management and welfare.